Appendix - ServiceLinker Configuration Diagram
info
- Reference Materials(click)
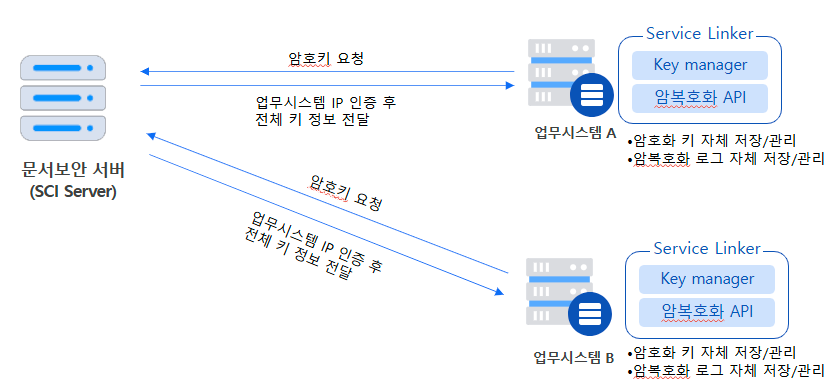
- Each business system requests an encryption key andBased on IPTransmission of the entire encryption key after approval on the SCI Server
- When developing a new work system (or new IP allocation), a new IP must be newly registered/approved to be used normally.
- Each business system performs in a daily batch.Daily full encryption keyRenewal / Receive and store in file format
- Store the entire encryption key for each business system.
- Performed encryption/decryption in each business system.Self-storage / Management of Logs
- Difficult to identify distribution channels as it was not delivered to the document security officer.