Proxy Relay Service
1. What is a relay proxy service?
Proxy Relay Serviceis a basic Proxy, a relay service that performs both Inbound and Outbound roles.
- Inbound Role: Relay requests for external users to access internal systems.
- Outbound Role: Relay for securely accessing external internet or SaaS services in an internal network (closed network, LGWAN, corporate network, etc.) environment.
It is designed to protect internal IPs by preventing internal devices from directly accessing the outside and allowing limited and secure external access only to specified URLs or SaaS.
Main Objectives
- Management of Control and Allowance Policies for External URL Access
- Blocking direct connections from the internal network to the external network
- Safe Use of External Services Based on RBI (Remote Browser Isolation)
- Protection of Internal Network IP/Network Information
- Management based on logs and policies when accessing external web.
2. Key Features
2.1 Outbound URL Access Management
- Pre-register external URLs and allow access only to permitted addresses.
- Blocked URLs are prohibited by the proxy service.
- Preventing indiscriminate access from the internal network to the external internet
2.2 IP Masking and Security Relay
- Internal clients do not connect directly to the outside.
- Only the relay proxy service and SHIELDGate communicate with the external network.
- Internal IP is not exposed to the outside.
2.4 Integrated Log and Access History Management
- Record which device accessed which URL
- Access Policy Violation Record
- Can be used for security audits and post-analysis.
2.5 External SaaS Utilization Mediation
- For example: ChatGPT, Google Workspace, MS365, collaboration tools, etc.
- Safe use of external SaaS even on internal networks
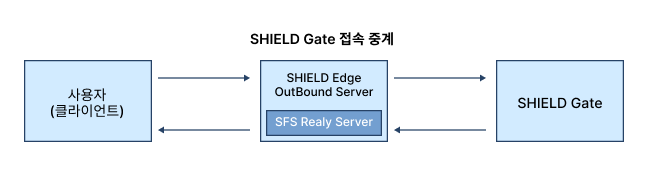
3. Concept Diagram of Relay Proxy Service

Description
- Inbound: Safely relay external user access requests to the internal system
- Outbound: Internal devices cannot directly access the external internet, andProxy Relay Serviceperforms external requests on behalf of
- Access to external internet services (including SHIELDGate) is only possible for URLs permitted by the proxy service.
- Includes SFS Relay Server functionality for RBI technology
- All information transmitted from the external environment is safely streamed in the order of SHIELDGate → SFS Relay → internal terminal.
4. Components and Roles
| Components | role |
|---|---|
| Basic Proxy | A proxy that performs both Inbound and Outbound roles, providing communication relay between internal and external, as well as URL access control features. |
| URL Policy Management Module | Allow/Block URL Registration and Policy Application |
| Authentication/Policy Engine | Access Control Management, Access Control |
| Logging Module | Access History and Policy Violation Records |
| Admin Console | URL Policy · SFS Settings · Log Management UI |
5. Relay Proxy Service Processing Flow
When using SHIELDGate cloud service (Outbound example)
Step 1. Register URL
The administrator registers the SHIELDGate URL and other necessary external site URLs in the relay proxy service console.
Step 2. Register Public IP (SFS Relay)
Register a public IP with the SFS Relay Server for using the Isolated Browser (RBI).
Step 3. Internal User Access Request
The user enters the registered URL (e.g., SHIELDGate URL) in the browser.
Step 4. Proxy Service Relay
The relay proxy service performs the following:
- Check URL Policy
- If it is a registered URL, external communication is allowed.
- Establishing a TLS session with an external SHIELDGate instead of an internal terminal
Step 5. RBI Screen Streaming
SHIELDGate safely runs actual websites from the outside, and
Streams only the screens rendered through the SFS Relay Server to internal devices.
Step 6. The internal terminal only receives the screen.
- The actual execution and scripts are not transmitted over the internal network.
- Maintaining Internal Network Security
6. Features of Relay Proxy Service (In/Outbound)
6.1 Enhanced Security
- Blocking Direct Connections Between Internal and External
- Protecting Internal IP
- Application of URL-based minimum privilege policy
- Blocking the Inflow of Malicious Scripts and Malicious Code
6.2 Management Efficiency
- Integrating Distributed External Access Policies into a Single System
- Access to SaaS services can be granted simply by registering a URL.
- Providing audit convenience through log integration management
6.3 Stable Connection Structure
- When an external service outage or network issue occurs, the proxy service can track the cause.
- Maintaining a steady flow of internet traffic on the internal network
6.4 Usable in Various Environments
- Local Government LGWAN
- Internal Network of Public Institutions
- Internal Security Zone of the Company
- External network blocking environment such as research institutes