Desktop Edge Deployment Guide
Caution
Table of Contents
- Server Installation and Server Configuration
- XMPP Installation and Configuration
- Admin Page Settings
- Appendix
1. Server Installation and Server Configuration
Open firewall information
-
The firewall distinguishes between information that is opened internally within the server and information that needs to be opened for external access.
-
Firewall Open Ports (Internal)
- 9090: Port for accessing the Openfire web console
- 5222: XMPP chat port (connection between server and work PC)
- 6222: SSH port (Work PC -> Server reverse connection)
- 8080 (80/443): Desktop Service Web server access port
- 9080: Desktop Service configuration page access port
-
Open Firewall Ports (External)
- 8080 (80/443): Desktop Service Web server access port
- 5222(Optional): open is required when using the public desktop, connection between the public desktop located externally and the server.
-
Check open firewall
$ sudo firewall-cmd --list-all
Check server installation package
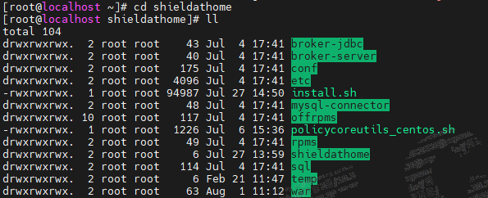
1) Copy (move) the shieldathome.tar.gz file to the /opt folder and extract it.
- Decompression command
$ sudo tar -xvf shieldathome.tar.gz
2) Move to the extracted shieldathome folder
- Check package installation status
Changing the SSH port
- default 22the SSH port of the port6222Change to port
1) Install policycoreUtils
- *CentOs family
$ sudo yum install -y policycoreUtils-python - *Ubuntu family
$ sudo apt-get install -y policycoreutils-python-utils - *Closed network environment
- Use the install file included in the package.
$ /opt/shieldathome/policycoreutils_centos.sh
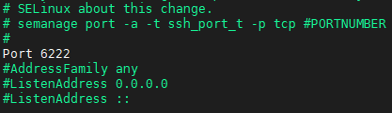
2) Change sshd configuration
- vi /etc/ssh/sshd_config
- #Port 22 > Port 6222 (port change history reflected)
- semanage port –a –t ssh_port_t –p tcp 6222 (Execute command to change to port 6222)
- service sshd restart
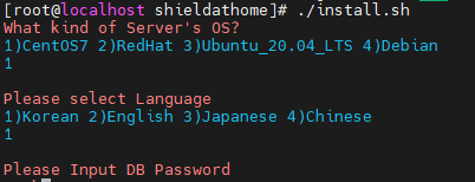
Run the server installation script
-
Move to the server package location and execute the installation script.
$ /opt/shieldathome/install.sh -
*After script execution
- OS Selection
- Database Language Selection
- Database Password Setting (Must be noted)
guacamole log rotate configuration
- Add logrotate configuration
$ vi /etc/logrotate.d/guacd
- Add the following content.
/var/log/guacd.log
{
daily
rotate 30
compress
missingok
dateext
notifempty
dateyesterday
}
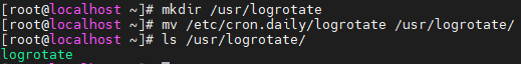
- Create a folder for the script and move files.
$ sudo mkdir /usr/logrotate$ sudo mv /etc/cron.daily/logrotate /usr/logrotate$ ls /usr/logrotate
- Check to see if it is displayed as shown in the image below.
- Add crontab configuration
$ crontab -e
- Add the following content.
0 0 * * * /usr/logrotate/logrotate
Replace SHIELDGate Desktop Agent files (if necessary)
- Move to the original file location
$ cd /opt/app/tomcat9/webapps/workathome/resources/new/
- Rename existing file (backup)
$ sudo mv SHIELDGateSetup.exe SHIELDGateSetup.exe_backup
- Move (copy) the new file to the existing file location after uploading.
- Change the name of the new file.
$ sudo mv 업로드파일명 SHIELDGateSetup.exe
Change server configuration file
- Change API service settings
$ sudo vi /opt/app/tomcat9/webapps/workathome/WEB-INF/classes/properties/server.properties
- jdbc.password
- Check if it has been entered correctly with the set password.
- internal.ipaddr=xxx.xxx.xxx.xxx
- Enter the internal IP of the server.
- SHIELDGate.OAuth.clientId
- SHIELDGate.OAuth.secretKey
- SHIELDGate.OAuth.masterExtra
- Entering information for the SHIELDGate app of the master tenant created in IdGP.
- SHIELDGate.OAuth.apiUrl
- Enter the IdGP server address.
- SHIELDGate.OAuth.extra
- Enter the company id of the registered company.
- SHIELDGate.OAuth.appClientId
- Enter the SHIELDGate app ID within the company.
- SHIELDGate.Oauth.logUrl
- Enter the integrated log server address.
- root.SHIELDGateUrl
- Enter the SHIELDGate server address.
- *Additional Settings
- Screen logger usage setting (use true, do not use false)
- dxl=false
- The upload path of *SHIELDGateSetup.exe is
/home/dxl/download/changed to
- root.useSrt
- Use of SRT
- Use - 1, Not in use (RDP) - 0
- Change Web Service Settings
$ vi /opt/app/tomcat9/webapps/workathome/resources/static/config.js
- VUE_APP_SHIELDGATE_URL
- Enter the SHIELDGate server address.
- Server Restart
$ sudo systemctl restart tomcat
Server Normal Operation Check & Configuration
{서버주소}:8080(Web service port) connection > Check if the page is displayed correctly
{서버주소}:9080Access the (Settings Page) > Click the "Login" button
데이터베이스Tab selection접속테스트Click the button to verify normal database connection.
웹서버Tab selection- Select whether to use SSL
- Upload the certificate file and enter the password when using.
.keystoreUsing the format file
- Select whether to use port forwarding
- Forwarding port when in use
443Input
- Forwarding port when in use
적용하기Button Click
- Select whether to use SSL
로그아웃Tab selection