Product Introduction
Why is the SHIELDEX File necessary?
Email attachments, file sharing services, cloud storage, etc.Malicious File InfluxThis is emerging as a major attack vector.
existingAntivirusIsandboxis the maliciousness of the fileDetectionin a way that,Zero-Day AttackIt is vulnerable to this variant of malware and requires continuous updates.
Approach to SHIELDEX File
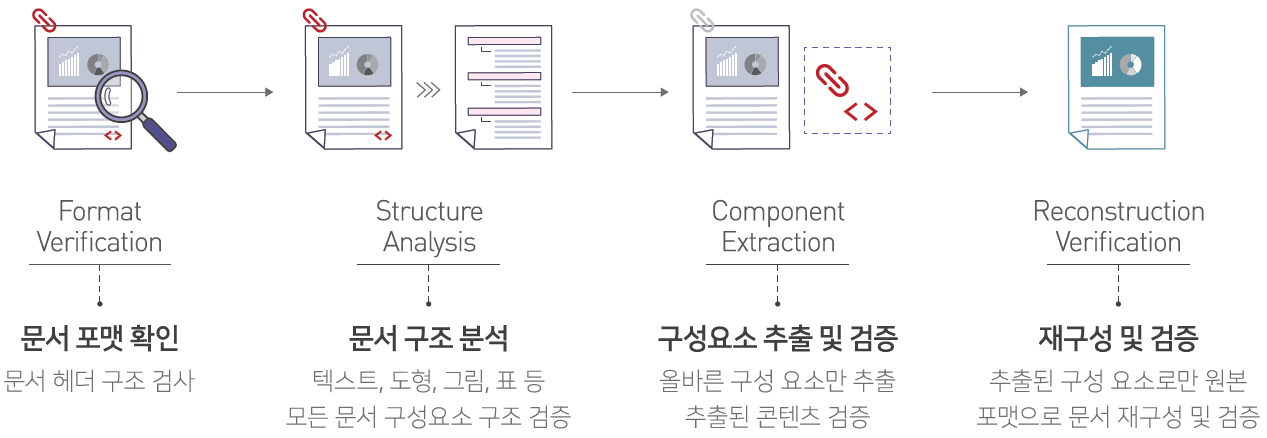
SHIELDEX Fileis not a detection method**CDR(Content Disarm & Reconstruction)Extraction and Reconstruction Method Based on**operates.
By extracting only safe content regardless of whether it is malicious, it is possible to block unknown threats in advance.
Processing Example
- Extension Spoofing Attack: By checking the document format, we block the infiltration of disguised malicious files where the extension does not match the actual file format.
- Macro-based attacksBlocks malware attacks that are automatically executed upon document opening by identifying macros.
- Script-based attacksIdentifies scripts such as JavaScript and VBScript to block phishing site links and malware download attacks.
- External Link-Based Attacks: Identifies external links and blocks automatic linking attacks to malicious sites.
- Steganography-based attacksIdentifies hidden malware in images to block malware execution attacks within image files.
CDR vs Existing Security Technologies
| item | Antivirus / Sandbox | CDR |
|---|---|---|
| Operating Principle | Signature / Behavior-Based Detection | Zero TrustBase Extraction and Reconstruction |
| Zero-Day Response | Detection failure possibility | Identify risk factors and extract only safe content for response. |
| Processing Speed | slowness | high |
| System Load | high | low |
| Update Dependencies | Signature DB update required | No update dependencies |
Key Features
| Features | Description |
|---|---|
| Zero-Day AttackResponse | Reconstruct files with safe content only to block unknown potential sources of risk. |
| High-Performance Processing | Fast processing based on a high-performance demining enginesandboxExecution process unnecessary) |
| Support for various formats | Support for a wide range of formats including MS Office, PDF, Hancom Office, HTML, JSON, images, and compressed files (ZIP/TAR/7Z). |
| Detailed Analysis | 6-Step Risk Visualization (Safe → Doubt → Warning → Danger → Serious →Tampering) andForensic DataProvision |
| Steganography Detection | Detection and Removal of Hidden Malware in Images |
| Flexible Policy Management | Support for detailed policies by file type, policies by user/group, and management of policy change history. |
Application Environment
- Email Gateway: Email Attachment Sanitization
- Web Gateway: File Download Neutralization via the Web
- Network interconnection environment: Sanitization during file transfer in a network-separated environment
- Cloud Storage: Cloud File Sharing Service Integration
- API Integration: Integration of various systems through REST API
Learn more
- Main Features: Complete list of provided features
- Application Scenarios: Real-world application cases and scenarios
- Administrator Guide: How to Use the Web Admin Console
- API Guide: How to Integrate REST API
- Glossary: Definition of Technical Terms